Digital Shadows: How Surveillance Firms Turn Your Phone Into a Secret Tracker

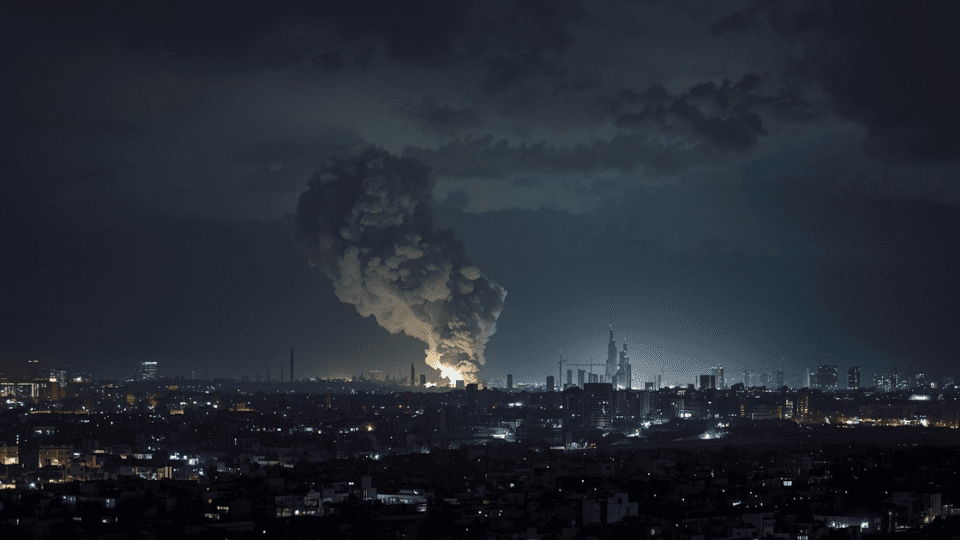
A group of digital spies just got caught in the act. Researchers from Citizen Lab recently uncovered a massive surveillance operation that uses the very networks we rely on for phone calls to track people’s locations. These surveillance vendors are not just hackers in a basement, they are companies that sell tracking services to governments. They abuse access to telecommunications providers to follow people across the globe, often without the phone company or the user knowing anything is wrong.
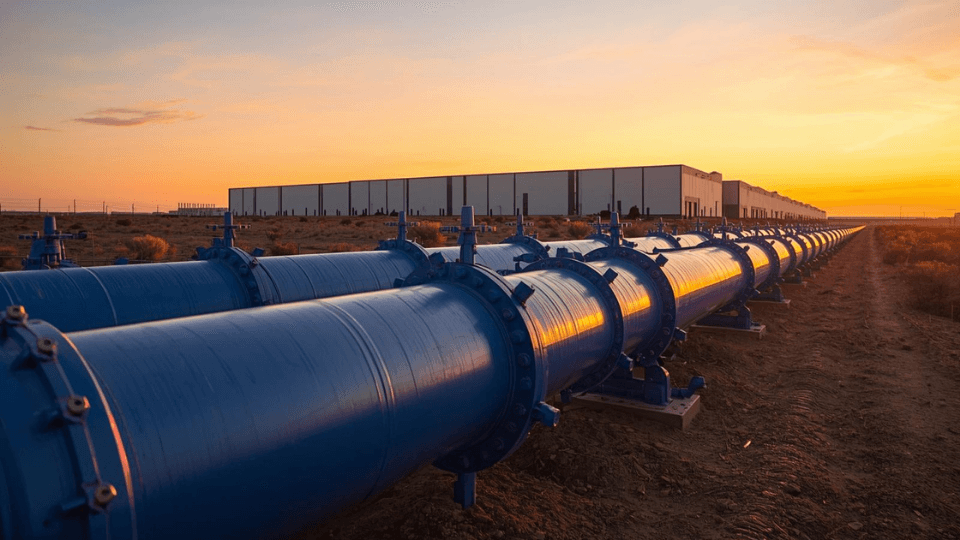
This discovery highlights a deep crack in the global phone system. For decades, mobile networks have relied on old protocols that were never built with modern security in mind. One of these is called SS7. It allows different phone companies to talk to each other so you can make calls while traveling. Because this system is so old and open, a company with the right access can send a “ping” to a phone and get its exact location. This essentially turns your personal device into a tracking beacon that follows you everywhere you go.
The Business of Invisible Tracking
The researchers identified two specific campaigns that have been running for years. These operations target high-profile individuals, including activists, journalists, and political figures. The surveillance firms behind these attacks do not need to install a virus on your phone. They simply exploit the plumbing of the internet. By gaining access to a single telecom provider in a smaller country, they can reach out and touch almost any phone on any network worldwide.
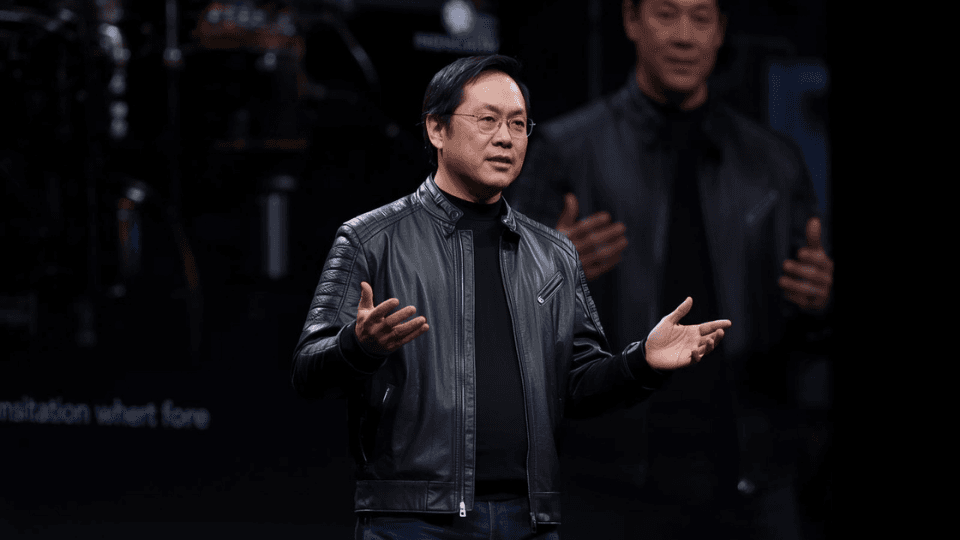
One of the companies mentioned in the report is a firm called Variston. They reportedly sold specialized tracking tools to government clients. While Variston claims their tools are for legal investigations, Citizen Lab found evidence that they were being used to stalk individuals across international borders. The success of these campaigns proves that the private surveillance market is booming. These firms make millions by finding and selling “zero-click” tracking methods that require no action from the victim.
Why Your 5G Phone Isn’t Safe Yet
You might think that upgrading to a 5G phone would solve this problem. While 5G does have better security features, the global network is still a mess of different technologies. Many 5G networks still fall back on older 4G or 3G systems to handle certain tasks. Spies know this and look for these “weakest links” to launch their attacks. If a 5G network is not set up perfectly, a surveillance vendor can still use the old SS7 tricks to find a target.
Phone companies are trying to fight back. Many have started installing “signaling firewalls” that are supposed to block these fake pings. However, the spies are smart. They constantly change their methods to bypass these filters. According to Citizen Lab, some of these surveillance campaigns have been running for over five years. This shows that the people doing the tracking are often one step ahead of the people trying to stop them.
Protecting the High-Profile Targets
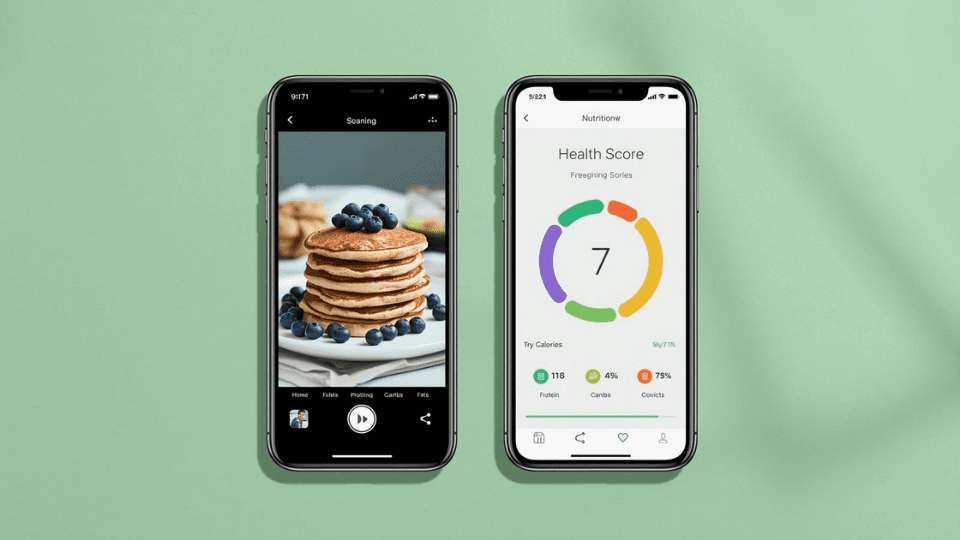
This type of tracking is not usually aimed at the average person. It is expensive and requires specialized access. But for “high-value” targets, it is a constant threat. Spies use “silent SMS” messages, which are texts that never show up on your screen, to trigger a location response from your phone. You would never know someone just tracked you to your home or office.
Citizen Lab warns that as long as we rely on these outdated network protocols, the problem will exist. Governments need to pass stricter rules on how telecom companies share access. We also need to move toward newer, more secure ways of handling mobile data. Until that happens, your phone’s location is only as private as the weakest network on the planet.